Black Hat Blues
GEEK MAFIA:
Black Hat Blues
GEEK
GEE MAFIA:
K MAFIA:
Mile Zero
Black Hat Blues
Rick Dakan
Geek Mafia: Black Hat Blues
By Rick Dakan
ISBN: 978-1-60486-088-7
LCN: 2009901383
Copyright © 2009 Rick Dakan
This edition copyright © 2009 PM Press
Al Rights Reserved
PM Press
PO Box 23912
Oakland, CA 94623
www.pmpress.org
Layout: Karl Kersplebedeb
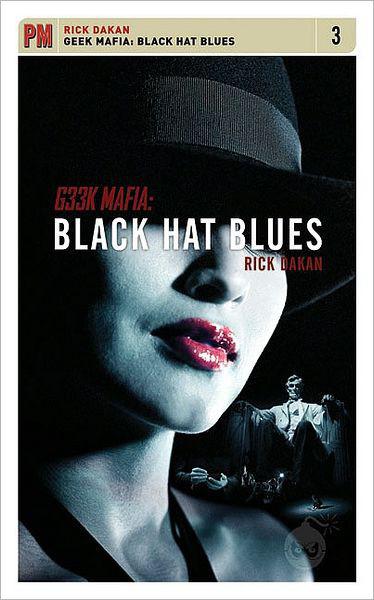
Cover: John Yates
Printed in the USA, on recycled paper.
This work is licensed under the Creative Commons Atrribution-Noncommercial-No
Derivative Works 3.0 License. To view a copy of this license, visit http://creativecommons.
org/licenses/by-nc-nd/3.0/ or send a letter to Creative Commons, 543 Howard Street, 5th
Floor, San Francisco, California, 94105, USA.
This is a work of fiction. Al characters in this book are fictional and events portrayed in this book are either products of the author’s imagination or used fictitiously.
Foreword
Thanks to All The Hackers
This is a work of fiction, so let’s keep that in mind, but it wouldn’t
have been possible to write this book without the welcoming, friendly,
helpful, and sometimes intimidating assistance of numerous real live
non-fictional hackers from all over the United States and Germany.
I spent the better part of a year traveling to hacker cons, interviewing
participants, attending talks, and taking copious notes. Almost without
exception the organizers, speakers, and attendees I talked to welcomed
me into the fold and helped me to, I think, really understand the world
of hacking. It’s a community I’ve come to love and now consider myself
a part of. So some of you out there might recognize yourselves in this
book, some of you are even mentioned by real name. In the latter case,
real names are used entirely fictitiously and shouldn’t be taken as real-
world reportage. Many other incidents herein might seem familiar to
those knowing few who were there for the real world events that inspired
them, and I hope you’ll get a smile or a thrill from my fictitious versions.
For everyone else, welcome to the world of hacker conventions. If
you’ve never heard of such a thing before (I certainly hadn’t until a
couple months before I attended my first), I encourage you to get online
and find out more. Watch some videos of some talks, check out some
websites, and if it looks interesting to you, try it out. What’s the worst
that could happen? Well, I guess this book is one version of the worst
that can happen, but really, you wouldn’t be this crazy, would you?
Paul
“I was going to, but even at this one I never log on using the wireless
at a hacker con, it’s like suicide, except your porn collection gets
stolen too.” Paul Reynolds smiled at the overheard bit of conversation
as he balanced three pizza boxes and two six-packs of Coke in front
of him and wove his way through the cluster of shivering smokers
huddled outside the hotel entrance. It was a relief to take the awk-
ward twirl through the revolving door and come in from the cold. No
one seemed to pay him or his pizzas any attention. This crowd had
seen a lot of pizza delivered in its collective lifetime. He picked up
more snatches of overheard data as he moved through the mostly male
conversation clusters that milled about the spacious and surprisingly
elegant hotel lobby with no purpose other than to meet, greet, and
discuss the topics of the day. “They have Jason Scott speaking oppo-
site Dan Kaminsky again… How many Shmoo balls are you going
to buy?… I actually kind of hate room parties… You have to try the
Ethiopian place this year… I’m thinking of not sleeping at all and
seeing if I actually start hallucinating in code.”
It was certainly the nicest hotel Paul had ever attended a hacker con-
vention in—usually they inhabited rundown economy chains out by
the local interstate—but the newly remodeled Wardman Park Marriott
in Washington D.C. catered to businessmen, politicians, and lobbyists
more often than hackers, and Paul imagined the con’s organizers prob-
ably sold it to the hotel staff as a “computer security conference” instead
of a “hacker con.” But looking around the crowd, he recognized the
quintessential types well enough after a year of moving among them.
2
Geek Mafia: Black Hat Blues
They were hackers: mostly male, casually dressed, lots of black t-shirts,
interesting hairstyle choices. Fewer had laptops than he’d first antici-
pated, but there were still more of them per capita than even a hotel
lobby catering to traveling business execs was used to. And a lot more
of those machines had stickers advocating various flavors of Linux or
BSD or proclaiming the owner’s allegiance in the great pirates vs. ninjas
debate. Paul came down firmly on the side of the pirates of course.
The con hadn’t even started yet, and Paul knew that there would be
hundreds more hackers arriving over the course of the evening, and
tomorrow morning the large ballrooms up the escalators would fill with
over a thousand people interested in hacking, hackers, or hacker cul-
ture. There would be parties, and arguments, and debates, and games,
and wildly entertaining rants mixed with droning, mind-sappingly dull
presentations. And unlike the previous cons he’d been to, this time he
would miss almost all of it. He wasn’t even registered to attend. In his
polo shirt, cardigan sweater and khakis he looked more like a vacation-
ing yuppie father of two toddlers than your typical con attendee, but
that was just his cover. Just like the con itself was providing cover for
why he was really in DC and what he and the Crew were planning.
Paul bypassed the throng waiting in front of the bank of elevators
and cut down the wide, carpeted hall past the Starbucks and the bar,
headed towards an unmarked door tucked into one corner. He balanced
one of the pizzas against his hip long enough to open the door to the
fire stairs and slipped inside with a last glance around to see if anyone
noticed him. No one he could see did. Inside and up five flights and
out again, an exertion that would have left him breathless a year or
two earlier. Down the hall to the right, and three quiet knocks on the
door. He saw someone’s head block the thin trickle of light through the
peephole and he shook his head slowly to the left and then the right.
Latches unlocked on the other side and the door opened. Chloe smiled
and ushered him and the pizzas inside.
He scanned the suite for some empty, pizza-box sized surface, but
found no likely candidates, so he placed them on top of the stacked
luggage in the corner to his right. The others didn’t look up from their
various pressing tasks, and Paul didn’t want to distract them. The food
would be there for them when they remembered they needed to eat.
“What’d I miss?” he asked Chloe, who apparently needed to eat right
now judging by the way she scooted past him and flipped open a box.
She was wearing a smartly tailored gray skirt-suit combo that showed
a little more thigh than might be considered strictly professional. Then
again, the bright pink, short cropped hair clashed with the jacket’s
Rick Dakan
3
stylish cut in an even less business-like manner. But Paul knew there
was a brown wig in a conservative cut lying on their bed that completed
the disguise.
“Which one’s mushroom?” Chloe asked.
“On the bottom I think.”
“Not much. Things are finally up and running downstairs so we’ve
got c1sman back with us. Their network’s up. Ours is up. The outside
connection is, and I quote, ‘mostly up,’ whatever that means.”
“And the hotel connection?”
“Waiting for the hotel IT guy to get slightly less paranoid or a lot
more tired. Are these mushrooms from a can?”
“Probably.”
“That sucks.”
Chloe took two slices anyway, and Paul turned to the rest of the room
just to make sure they realized food was here. “Pizza,” he said in a loud
clear voice. At the desk across the room a slightly pudgy, Asian woman
sporting a practical ponytail and jeans bent over a soldering iron and
cheap digital camera that she’d taken apart. Bee didn’t look up. Sandee,
a lithe, athletic man with soft, strong features, a silk kimono, and just
enough make-up on his nut brown skin to make him beautiful, reclined
in the chair in the corner behind her, He smiled up from behind his
laptop at Paul and nodded, but he never ate pizza. Spread out on the
couch in front of three flat panel displays on the coffee table and the
rack of computers on the floor beside him was a pear shaped man with
a scraggly light brown beard and a black t-shirt. His eyes flicked up to
Paul, back to the screen, up to Paul, back to the screen, towards the
pizza, and then rested on the screen. “Um, thanks,” he said. “Cool.”
He typed. “Thanks.”
Paul could see how nervous he was. This was all new to him. Well
not
all
new. The hacking was old hat. Hacking as part of an elaborate
scheme to ruin someone’s life was the new part. He glanced at Chloe
and she twisted her mouth into unspoken agreement with his analysis.
Paul went over and took a seat on the couch. “Alright, c1sman, walk
me through this. Where are we at?”
“We’re in the weeds, buddy,” c1sman said. He had a mild southern
accent to his deep voice, and Paul thought he sensed a slight quavering.
He was tired of course. He probably hadn’t slept for two, maybe three
very busy days.
“It’s not the weeds,” Paul assured him. “It’s the tall grass. We’re in
the tall grass and they don’t see us coming. So walk me through it.
Where we at?”
4
Geek Mafia: Black Hat Blues
C1sman dragged his top teeth across his bottom lip, pulling on some
stray beard hairs and then turned back to the screen. “Well, it took
longer to get the con’s wireless up and running and the other volunteers
and me got into a little bit of a tussle over some setup issues but then we
figured it out. It was like you said, they were so busy dealing with all the
real problems of setting up a massive open network in a couple days that
they didn’t notice my little additions. And really we were almost totally
screwed because for, like, two or three hours, even I wasn’t sure we’d
get it up running. And then I thought it was my stuff—our stuff, the
thing for our thing, I mean, that was screwing things up, but it wasn’t.
It was something that should’ve been just obvious because we’re all
tired, right? So anyway, it wasn’t me. Us. And I’ve just checked on it and
we’re up and running piggybacked on the con’s connection and running
through the new TOR clusters that we—the con staff I mean—set up
for the demo tomorrow.”
“So we’re set,” said Paul, wanting to be sure that The Onion Router
(TOR) set-up was working right since it was crucial to their plans.
An onion router is a cluster of computers that users can connect to
the internet through, routing the signal around various machines in a
way that makes it almost impossible to trace them back to their origin.
Almost impossible, and c1sman had come up with some innovations for
making it even closer to impossible, even if someone was monitoring
the traffic as it came in and out of the the TOR.
“We’re set on the anonymizer front, yeah. And we’ve got about half
the bandwidth I’d want to really spread things out a little more than
that. My little beasties are all in place and as of my last check… well,
let’s see here…” c1sman—pronounced sis-man, as in system admin—
typed on one of the console windows open on the middle screen in front
of him. A table of numbers and letters streamed past and Paul saw what
he recognized as a long list of IP addresses flowing by. These were the
addresses of the computers in the botnet that c1sman had built up over